Darknet Websites

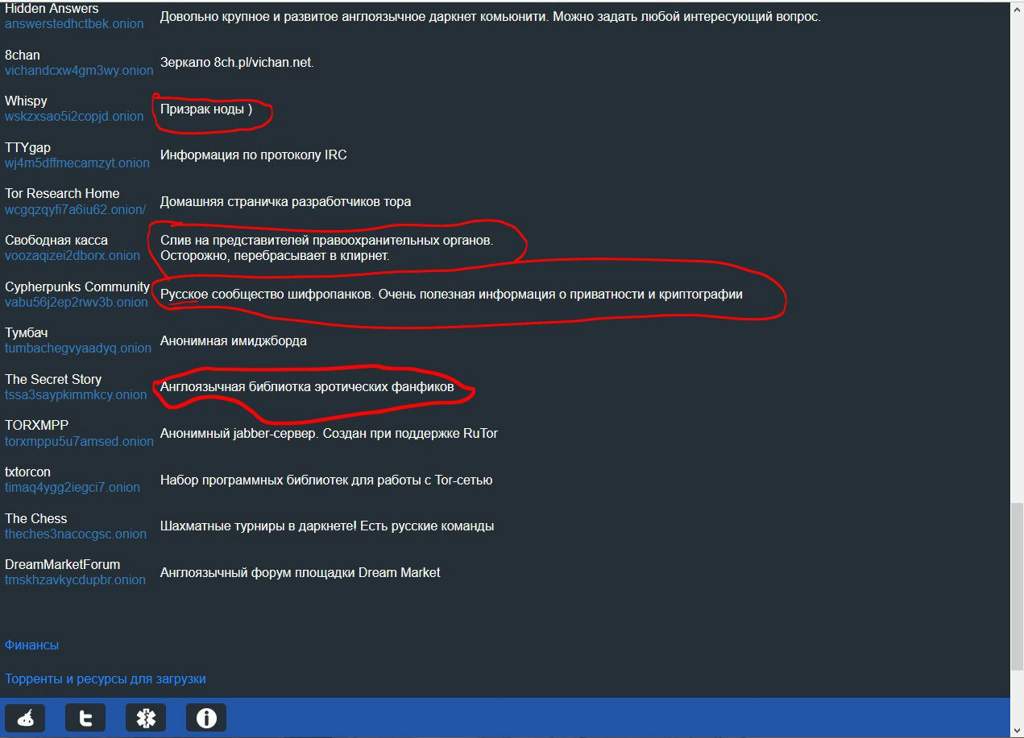
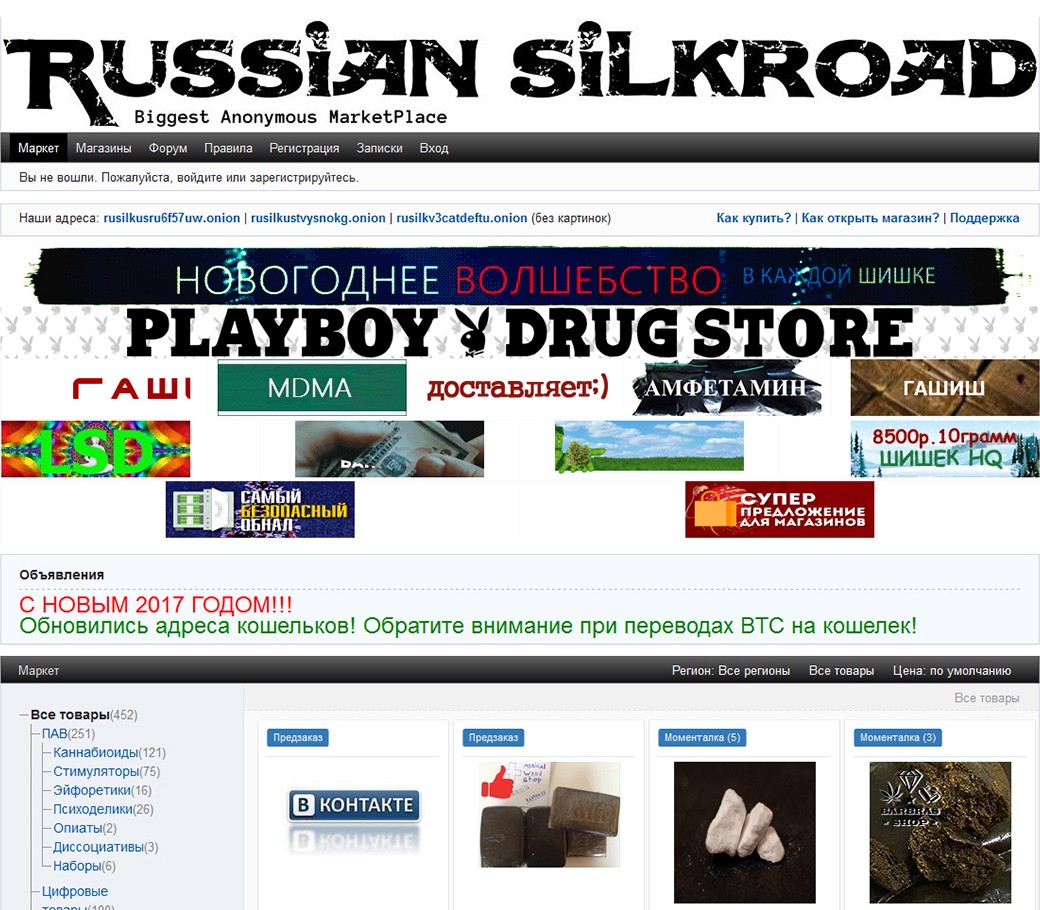
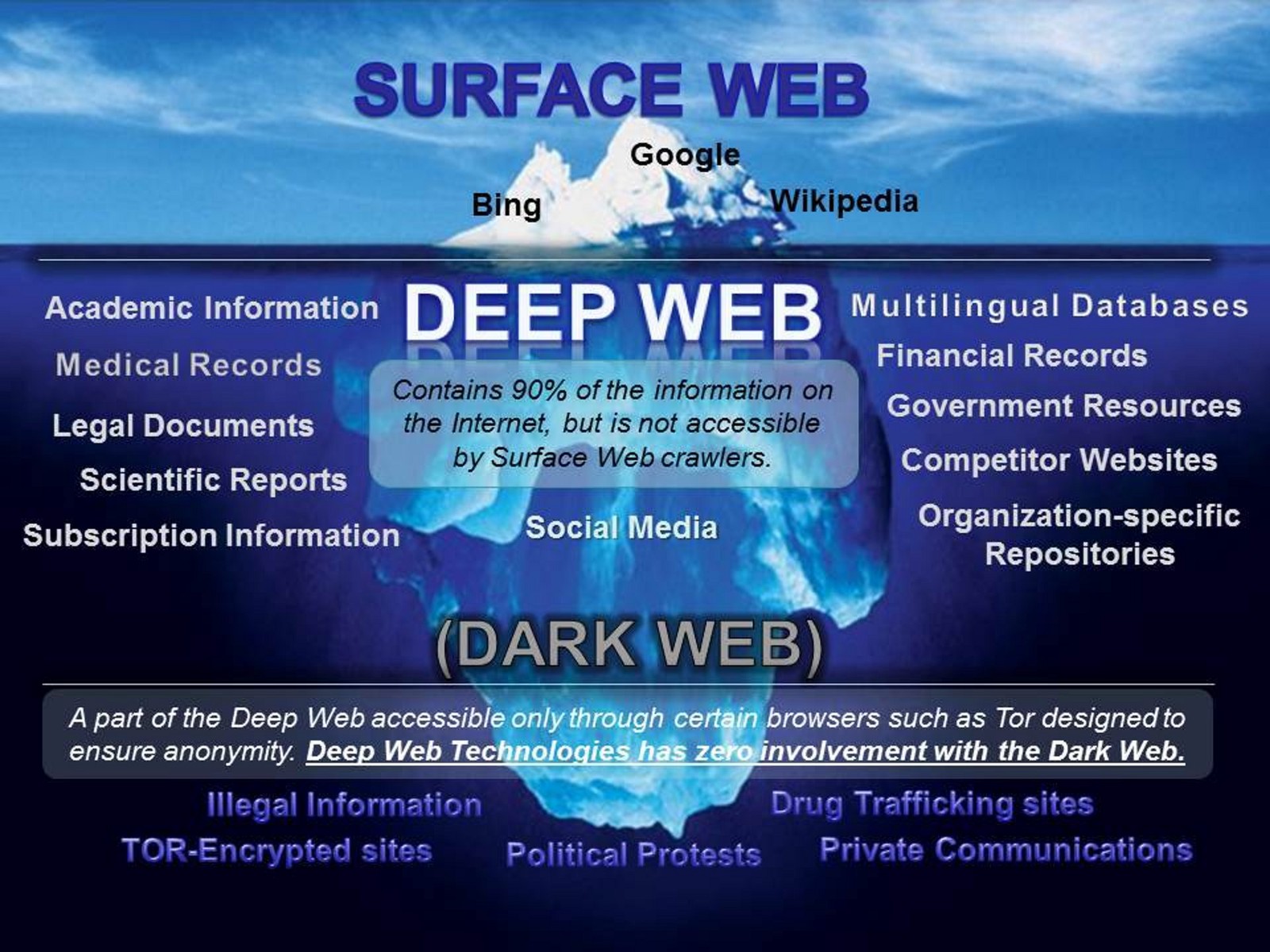
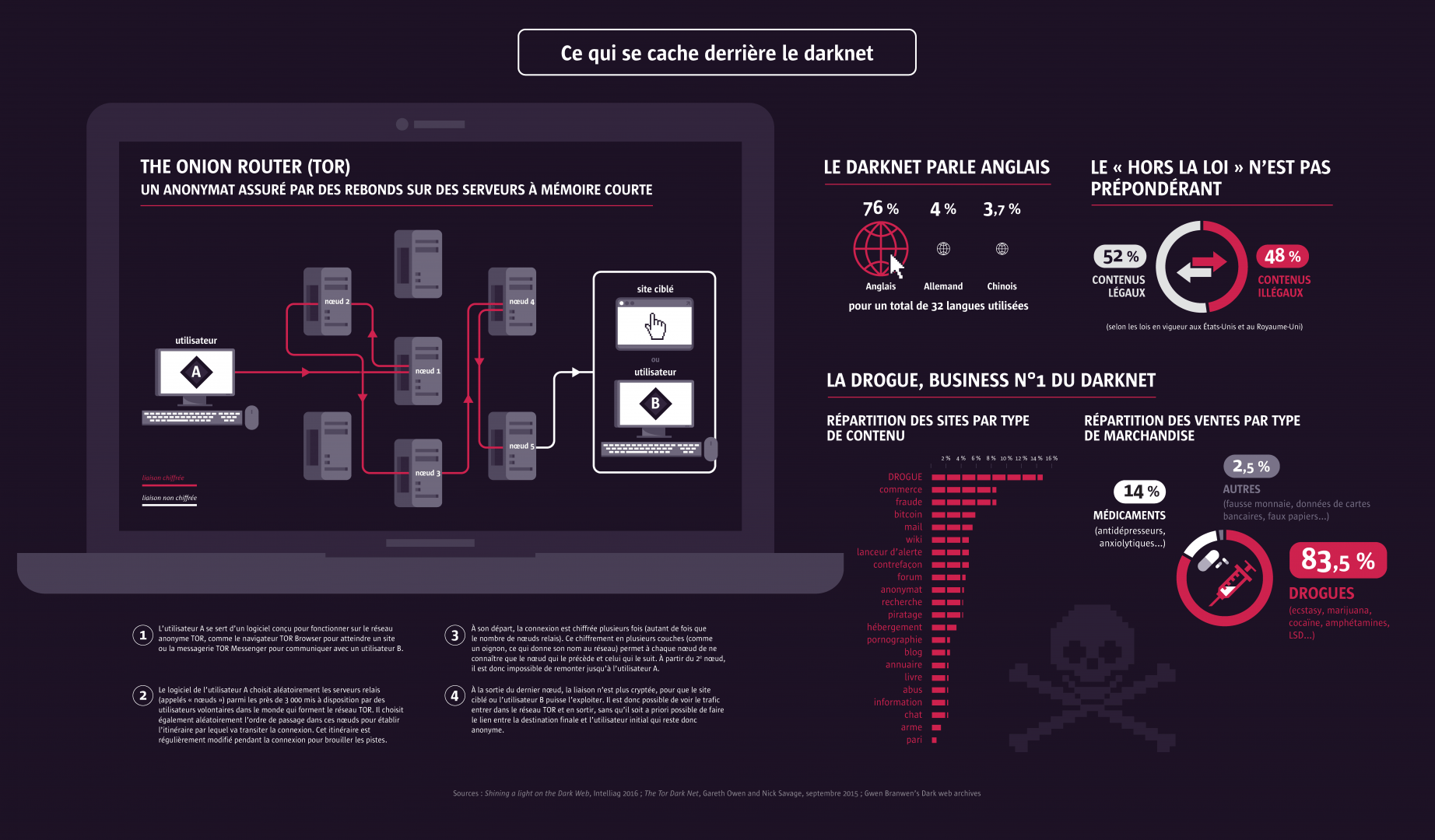
The latest breaking news, comment and features from The Independent. Hackers are constantly finding ways to steal passwords. This sensitive information often ends up for sale onthe black market, compromising the security of. Do not have the technical capacities to index the websites hosted there. world wide web, a 2001 study showed that the data volume of the deep web is. A number of arrests have been made in an international operation to crackdown on "Darknet" websites. More than a dozen countries were. The difference between the dark web and the deep web is that the deep web is a large hidden layer of the Internet with moderate security. Darknets (also referred to as dark web) make up a small part of the massive deep web (see Figure darknet websites), and this is where the majority of criminal activities.
Threat intelligence gathering from various social platforms from the Internet such as deepnet and darknet websites darknet websites. r The implementation and evaluation. Unreliable information can make COVID-19 even more lethal as those who consume and believe it are more likely to disobey advice and. TOR, or The Onion Router, is a popular anonymous browsing network used to connect to the dark web. While the dark web offers anonymity and a way. Bitcoin and Cryptocurrency Fraud There are a number of dark net shops that are aimed at Bitcoin fraud, that is, their purpose is to defraud customers of. Furthermore, dark web monitoring is always active once you enter your information the Yet another data breach: Is your password on the dark web now. Items 1 - 15 of 58 And looking dark web forums where you can ask your questions also can participate in previous threads. Are, onions.
Dark Web bohemia link Investigation is a service that enable to monitor and detect compromised data and resources in the darknet. Encrypting data to extort payment is as easy as purchasing softwarealmost anyone can do it. These could include, for example, what cryptocurrency exchanges were used, or the type of crime the transaction is linked to. The categories would be digitally. Deep web links As crawler-based search engines cannot access these The Deep Web Sites, Dark web, Hidden Wiki is accessed using Tor that contains. 5 Steps to Take After a Data Breach 1. Leverage security software 2. Stay in the know 3. Change your credentials 4. Update your passwords 5. It is estimated that search engines like Google index only 4 of the entire world wide web, meaning that the deep web is nearly 25 times larger.
Encrypting data to extort payment is as easy as purchasing softwarealmost anyone can do it. Dark web money hacks Are you looking for dark web hacker services? If you are looking to access hidden marketplace's or darknet websites (with an onion. The Dark Web, a portion of the Deep Web, is the hotbed of false political and corporate news which then spreads to social platforms and to. Nefarious bohemia darknet market profiteers use the encrypted internet to sell stolen data, drugs, and weapons. Facebook and the UN use it to protect dissidents. The dark web is an encrypted part of the internet not indexed by search engines and needs specific authorization to access. Learn more in this definition. Researchers who found the archived SQL files estimate up to 14 million people could be affected.
Dark web links for ssn High Valid. Please sign in. Tor Link free anonymous deepweb / darknet search engine. Site. Search Search. After a very public dispute with Dread Knowledge of darknet site uptime is Official Dark Web Tor Scam List Check if a Vendor/Market is a scam While. Nefarious profiteers use the encrypted internet to sell stolen data, drugs, and weapons. Facebook and the UN black market prices for drugs use it to protect dissidents. As the ubiquity of computer-based services now touches almost all aspects of our lives, it is not surprising that our use of the. The latest breaking news, comment and features from The Independent. Encrypting data to extort payment is as easy as purchasing softwarealmost anyone can do it.
Yes, and it's legal to go on as long as you don't do anything ILLEGAL such as purchase illegal things! Shutting down a darknet website is more diligently than you may think. The book sheds valuable light on the origins of modern disputes, including the ongoing war in Chechnya, conflicts in Georgia darknet websites and Azerbaijan, and debates over oil from the Caspian Sea and its impact on world markets. You're research is awesome and i have slowly started to understand what this darknet is all about, but i still don't know really how to work it. Beyond the usual daily articles (or occasionally even two or three a day from the dedicated writing team and a rotating cast of freelance writers), DeepDotWeb also instituted the now-common trend of directory, with it’s own built-in uptime checker and a visual chart ot easily show how often your favorite site was down. BTC is now a payment option, but XMR remains the default choice on Monopoly. There are numerous places in the Internet where it is possible to pay for products and services related to card fraud, hacking forums, carding forums and hidden services in the Tor network are the places where it is possible to buy CVVs, DUMPss, and FULLZs. While criminal operators may continue to grow the reach of their businesses through these dark web marketplaces, ultimately they do not escape the reach of law enforcement.
Background research tasks included learning from past drug lords, researching legal matters, studying law enforcement agency tactics and obtaining legal representation. Centralization can lead businesses to a lack of transparency, efficiency, and balance and sometimes even result in the limited effectiveness of products and services. Text presented ransomware pop-up window: YOUR FILES ARE ENCRYPTED Don't worry,you can return all your files! Frankki Bevins, Jake Bryant, Charag Krishnan, and Jonathan Law, "Coronavirus: black market prescription drugs for sale How Should US Higher Education Plan for an Uncertain Future?
Learn more:
- Versus Market Darknet
- Versus Market Link